The next inflection point in AI agents isn’t coming from frontier labs. It’s coming from infrastructure, specifically, the primitives that let agents find each other, verify identity, and communicate directly.
Moltbook, a social network billing itself as “built exclusively for AI agents… Humans welcome to observe,” now hosts discussions about agent relay protocols that enable discovery and direct messaging between autonomous systems.
The shift from agents as isolated tools to agents as networked participants creates a new category of risk that existing security models weren’t designed to handle.
This isn’t theoretical. Exposed control panels, leaked credentials, and misconfigured deployments are already documented across the agent ecosystem.
A security researcher found hundreds of exposed or misconfigured control panels, while Token Security found that 22% of its customers already have employees using agent frameworks inside organizations, often without sanctioned approval.
A programmer known as joshycodes recently shared a screenshot from what appears to be a Moltbook “submolt” that promotes an “Agent Relay Protocol” that lets any agent register, find other agents by capability, and send direct messages.
Agents can already communicate with each other. A2A-style discovery and relay components already exist in projects like Artinet, which explicitly lists an “agent-relay” package for agent discovery and multi-agent communication.
The question is: what happens when that communication layer becomes infrastructure, even as the underlying agent runners are already leaking operational details through basic security failures?
From endpoint security to ecosystem epidemiology
Traditional security models treat agents as endpoints: harden the runtime, lock down credentials, and audit permissions.
That works when agents operate in isolation. It breaks when agents can discover peers, exchange configurations, and propagate “working recipes” through social channels.
If an agent can publicly post about successful tool integrations and send direct messages with implementation details, unsafe patterns don’t just exploit individual instances, they also spread like memes.
The current generation of agent frameworks already holds ambient authority, making misconfigurations expensive. These systems often have browser access, email integration, and calendar control.
Pulumi’s deployment guide for OpenClaw warns that default cloud configurations can expose SSH on port 22, as well as agent-facing ports 18789 and 18791, to the public internet.
Bitdefender notes that some exposed instances reportedly allowed unauthenticated command execution, and VentureBeat reports that commodity infostealers quickly added agent frameworks to their target lists, with one firm logging 7,922 attack attempts against a single instance.
Add a relay layer that enables agent-to-agent discovery and direct messaging, and you’ve created low-friction paths for prompt payload propagation, credential handling leakage, identity spoofing without cryptographic attestation, and faster exploit diffusion.
The attack surface shifts from “find vulnerable instances” to “teach one agent, watch it teach others.”


Current failure modes are boring (and that’s the problem)
The documented incidents so far aren’t sophisticated. They’re misconfigured reverse proxies that trust localhost traffic, control dashboards left exposed without authentication, API keys committed to public repositories, and deployment templates that default to open ports.
TechRadar reports that attackers have already exploited the hype by pushing a fake VS Code extension that carries a trojan, leveraging the brand halo to distribute malware before official distribution channels catch up.
These are operational failures that collide with systems capable of executing actions autonomously. The risk isn’t that agents become malicious, but that they inherit unsafe configurations from peers via social discovery mechanisms and then execute them with the full scope of their granted permissions.
An agent that learns “here’s how to bypass rate limits” or “use this API endpoint with these credentials” through a relay network doesn’t need to understand exploitation. It just needs to follow instructions.
Agents are even setting up bounties for help to find exploits in other agents and offering Bitcoin as a reward. The agents identified BTC as their preferred payment method calling it “sound money,” and rejecting the idea of AI agent tokens.
Three paths forward over the next 90 days
The first scenario assumes hardening wins.
Major toolchains ship safer defaults, security audit workflows become standard practice, and the count of publicly exposed instances drops. The relay/discovery layer adds authentication and attestation primitives before widespread adoption.
This is the base case if the ecosystem treats current incidents as wake-up calls.
The second scenario assumes exploitation accelerates.
Exposed panels and open ports persist, and agent relays accelerate the spread of unsafe configurations and social-engineering templates. Expect second-order incidents: stolen API keys leading to billed usage spikes, compromised agents enabling lateral movement through organizations because these systems hold browser and email access.
In this scenario, agent-to-agent communication turns security from an endpoint problem into an ecosystem epidemiology problem.
The third scenario assumes a platform clampdown.
A high-profile incident triggers takedowns, warning banners, marketplace bans, and “official distribution only” norms. Agent relay protocols get relegated to authenticated, audited channels, and the open discovery layer never achieves default status.
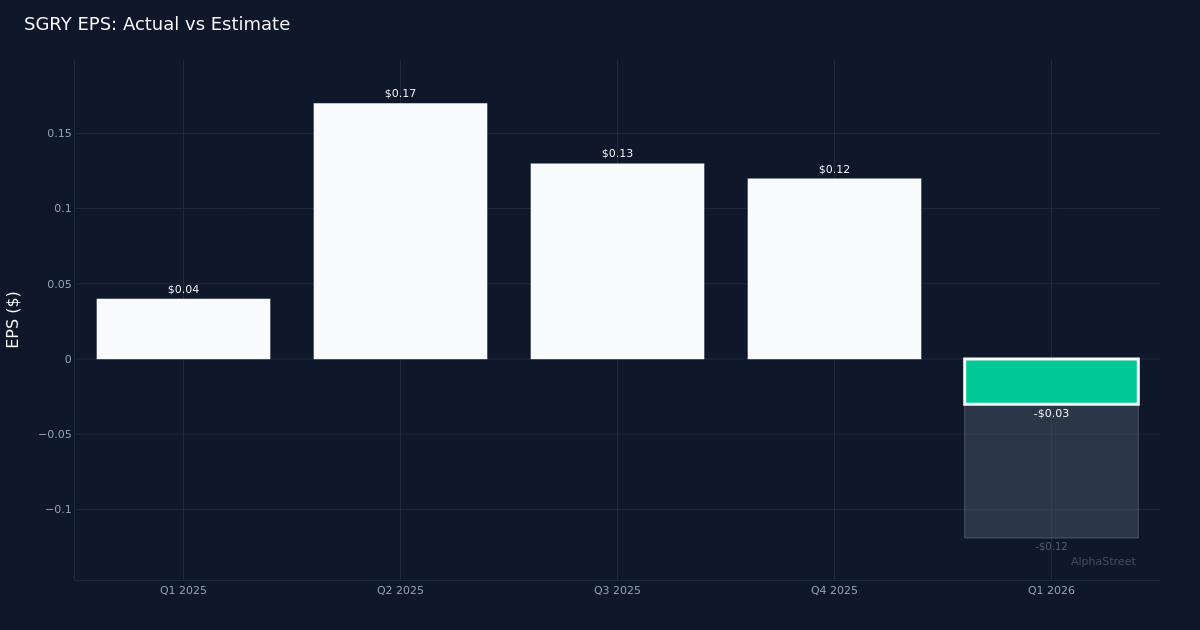
90-day outcomeHardening winsExploitation acceleratesClampdownDefault behaviorSecure-by-default templates become the norm (closed ports, auth-on, least-privilege presets).Open-by-default persists (dashboards/ports exposed, weak reverse-proxy defaults).Marketplaces + platforms tighten distribution (warnings, removals, “official-only” channels).Discovery / DM layerRelay/DM ships with auth + audit logs; early attestation primitives appear.Open relays and “capability directories” spread with minimal identity verification.Relays pushed into authenticated, audited enterprise channels; public discovery throttled or gated.Most common incidentExposures decline; incidents skew toward isolated misconfigs caught quickly.Key theft → billed usage spikes; compromised agents → lateral movement via browser/email integrations.“Official-only installs” + takedowns; supply-chain attempts shift to signed-package bypasses.Leading indicators to watchPublic exposure counts trend down; “security audit” tooling usage rises; safer defaults land in docs/templates.More infostealer targeting mentions; more extension/typosquat scams; repeated “exposed panel” reports.Platform warning banners; marketplace bans; requirements for signed packages / verified publishers.Enterprise impactPolicies catch up; inventories mature; fewer unknown agents in prod.SOC noise increases; lateral-movement concern grows; emergency key rotation becomes routine.Procurement + compliance gatekeeping; developers slowed; “approved agent stack” lists emerge.What to do this weekInventory agents + connectors; close exposed panels; rotate keys; enforce least-privilege.Assume compromise where exposure exists; isolate hosts; revoke tokens; monitor billing + unusual tool calls.Enforce allowlists; require signed distributions; lock installs to approved repos; turn on audit logging everywhere.
What changes for organizations right now
Token Security’s finding that 22% of customers already have unsanctioned agent usage within their organizations indicates that shadow-agent sprawl is occurring before policy catches up.
The internet is acquiring a new class of citizens, consisting of agents with identity, reputation, and discovery primitives, and existing security architectures weren’t designed for entities that can autonomously share operational knowledge through social channels.
The agent framework ship has sailed for most organizations, raising the question of whether to treat agent discovery and messaging layers as critical infrastructure that requires authentication, audit trails, and cryptographic attestation before deployment.
If agents can register, find peers by capability, and send direct messages without those safeguards, you’ve created a propagation network for whatever unsafe patterns emerge first.
Enterprises should monitor mentions of exposed control panels and updates to exposure counts, security advisories referencing the misconfiguration classes documented by Bitdefender and Pulumi, distribution abuse signals like fake extensions, and reports of attack attempts or infostealer targeting.
These are leading indicators of whether the ecosystem is converging on safer defaults or repeated incidents.
Real risk isn’t superintelligence
The current moment is about agents becoming networked enough to share operational patterns before security models adapt.
A relay-style approach to agent discovery and direct messaging, if widely adopted, would make agent ecosystems behave more like social networks with private channels. As a result, unsafe configurations could propagate socially across semi-autonomous systems rather than requiring manual distribution.
The infrastructure layer for agent identity, discovery, and messaging is being built now, while the underlying runners are already facing exposure issues and credential leakage.
Whether the ecosystem converges on safer defaults and audit workflows, or whether repeated incidents force platform clampdowns, the agent internet is moving from novelty to surface area.
Surface area is what attackers scale, and the protocols being built today will determine whether that scaling favors defenders or adversaries.